Every administrator is afraid about Ransomware software. We want to protect our systems with so many different approaches and at many layers, but almost always we try to use complicate techniques to archive basic objectives. I found on
TechNet an article, which sounds good for me and I am also confidential using Windows embedded functionalities for trying to prevent an attack.
Are there positive and negative sides? Of course they are, the most important negative thing I recognize is that we are using technology based on file type. Actually we are trying to prevent to write all known file extensions that can be written on our system. This will work if we know the extension and we have to search for new used file extensions and add them as blocked file types. But there are also positive things: we don’t need to buy anything, we have all we need ready on our server – we have just to use it! It is very simple to configure and maintain and it works!
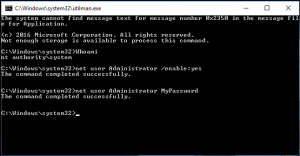
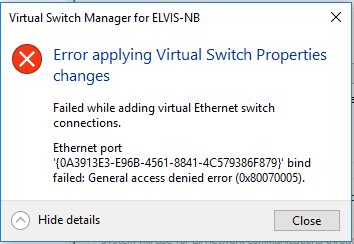
When I read this article, I was surprised why I have to do all those steps thru GUI? We can simply use PowerShell that is quicker and it will do exactly the same things every time we will start it. Well, I made a script that you can run on every server you have to protect and for every share or partition you want to protect. There is only one think that you cannot protect: system drive if you try to prevent whole drive. In this case, the protection will be passive and not active and there is no way to change it (but I hope that you don’t share system drive).
Things that you have to know are basic, just few data:
- Path to protect
- SMTP server for sending mail (and be careful with authentication! Test it!)
- Mail address form which mail will be sent
- Mail address from administrator
- Script that you want to run after detection (if you want)
You can run it as many times you want, on every server you want (version 2008 and newer) and you will be able to protect your data. It is a secure way to do it because you just prevent to change the data transformation and not the malware itself. I recommend also to use a script published on TechNet article for disabling the AD user or deny user access to server (It is also zipped into my file; including subinacl.msi).
To prevent malware, you can use an additional build in function: AppLocker and also this is explained here. And by the way, the approach is tested on Server 2016 TP5 – it’s working!
Enjoy!